Top 10 Globally Recognized Certifications for Cyber Security
U-Next
SEPTEMBER 27, 2022
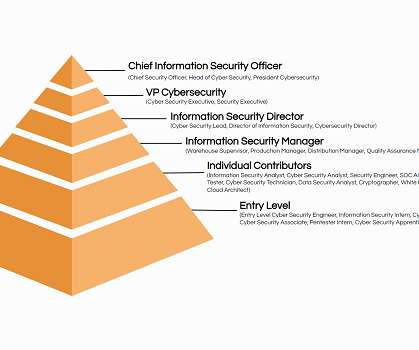
Cybersecurity or computer security and information security is the act of preventing theft, damage, loss, or unauthorized access to computers, networks, and data. Cybersecurity certifications authenticate your skills and reflect that you have mastered the subject presented in training. Administrator of Security .

















































Let's personalize your content