What Are SOC and NOC In Cyber Security? What’s the Difference?
U-Next
FEBRUARY 27, 2023
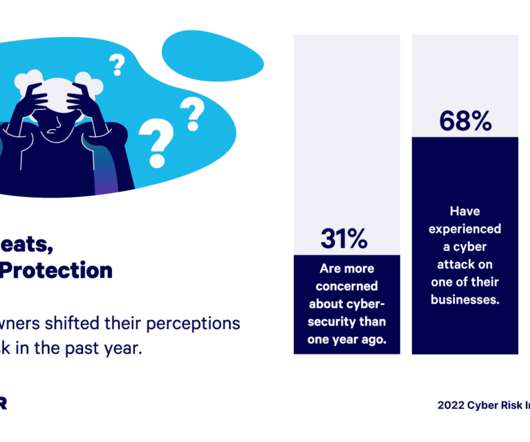
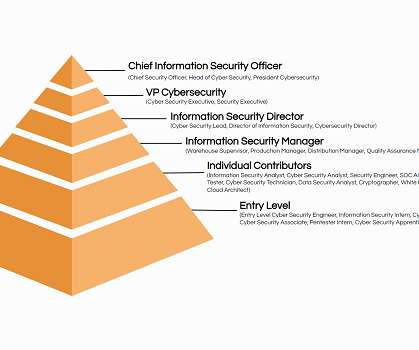
By 2027, the cybersecurity market is anticipated to expand at a CAGR of 13.37%. Security Operations Centre (SOC) and Network Operations Centre (NOC) are key positions in any cyber security team. In the world of cyber security, NOCs play an important role in detecting and responding to security operations and incidents.
















































Let's personalize your content